How to Spot a Phishing Email
A new well-designed phishing email has been aimed at cPanel users recently, and we want to help our users stay safe.
What is Phishing?
Phishing, by definition, is the act of attempting to acquire information such as usernames, passwords, and credit card details by masquerading as a trustworthy entity in an electronic communication such as email. The most effective phishing emails make use of e-mail spoofing, where the ‘from’ address that your mail clients display seems to be valid. These emails will include a link that directs users to enter details at a fake website. Fake websites can have the same look-and-feel as the legitimate one and can fool an unsuspecting user.
How Phishing Emails Affect Email Users
cPanel powers more than a third of the websites on the internet making cPanel users an obvious target. Taking steps to defend against some of the most obvious offenders using SPF records helps but doesn’t prevent all attacks. Education, reporting, and mitigation are key to preventing the effectiveness of these attacks.
What to do if you get a Phishing Email
The first step to take if you think you’ve received a phishing email is to confirm it.
- Check the email headers of the ‘Sender’ address
- Here is a knowledgebase article on how to find headers in different email applications
- These headers include all kinds of information, so don’t worry if not all of it makes sense.
- Check for links, logos, typos included in the email
- Typos, misspellings, and incorrect capitalization (e.g., CPanel or Cpanel, vs. the correct cPanel) are red flags
- URLs or names that aren’t quite right (e.g., cpanelcom.com therealcpanel.com) are red flags
- Report the email and the URL
- Report the URL to http://www.google.com/safebrowsing/report_phish/
- Reporting will block the URL in Chrome, Firefox, Android, iPhone, Google, and more
- Report the URL to https://www.microsoft.com/en-us/wdsi/support/report-unsafe-site
- Reporting will block the URL in Edge, Office 365, and Internet Explorer
- Forward the email, including the full headers, to reportphishing@apwg.org
- DO NOT forward any attachments!
- There are a ton more steps you can take to help prevent this from impacting anyone else
- Report the URL to http://www.google.com/safebrowsing/report_phish/
What do they look like?
An example of a very well designed phishing email is below.
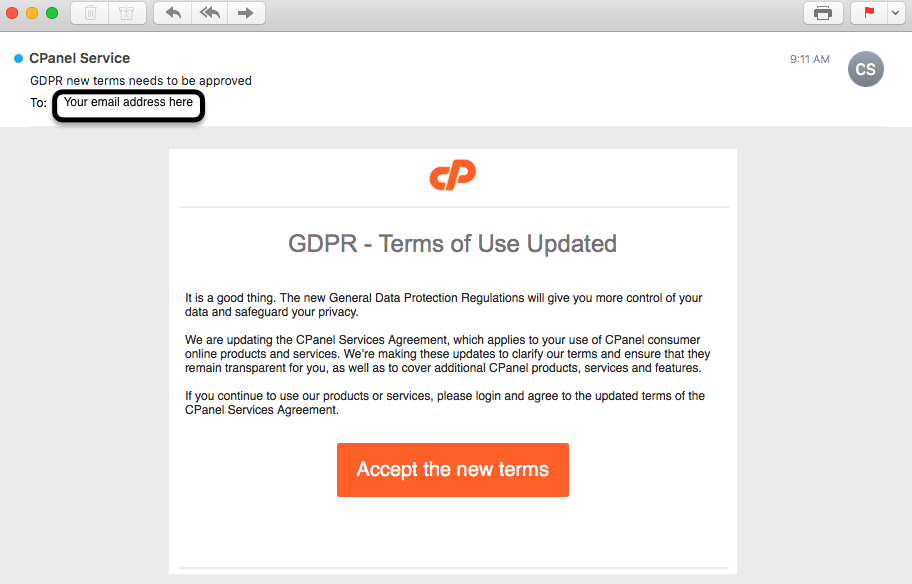
Notice that the content has very few typos, but the ‘from’ address has an incorrectly capitalized If you were to click on the ‘Accept the new terms’ button, you would be taken to a legitimate-looking form that appeared to be a cPanel login page, but the URL didn’t have cPanel anywhere it in.
Oh, no! I put my credentials in there!
If you fell for this trick (as many have), the first step is to change the password for the impacted account. If you have used that password anywhere else, change your password there, too. Then make a plan to sign up for a password manager and start making unique passwords for each account you have.
To recap
Phishing attacks…
- Often use spoofed email addresses in an attempt to trick the recipient into believing they are coming from a legitimate entity.
- Will send users to a site that has a legitimate design, and ask for a user’s login, password, other personal details.
- Should be reported to help reduce their reach.
If you spot a phishing email, report it! If you spot a phishing email that claims to be from a legitimate website or wants to direct you to a login page, report it and then send that email to: support@alpineweb.com with the full headers. That way we can help track and report it as well. Please do not forward any attachments!